Date:2026-04-16 Click:
Since 2025, Dr. Zhao Ruoyu, a young faculty member at the School of Computer Science and Artificial Intelligence, has been continuously forging ahead in cutting-edge areas of computer science. His research findings, as first author or corresponding author, have been successively published in top-tier international journals in the field of computer science, including ACM CSUR (impact factor 28, designated as a Category A journal by JUFE), IEEE TIP (CCFA、designated as a Category A journal by JUFE), TDSC (CCFA、designated as a Category A journal by JUFE), TSC (CCFA、designated as a Category A journal by JUFE), TMM (CCFB、designated as a Category B+ journal by JUFE), and TCSVT (CCFB、designated as a Category B+ journal by JUFE). This demonstrates robust research capabilities and innovative vitality, injecting new momentum into the scientific research endeavors of both JUFE and the school.
Building from a strategic height, we systematically constructed a knowledge graph for visual privacy protection.
Recently, the paper "Visual Content Privacy Protection: A Survey," with Dr. Zhao Ruoyu as the first author, was published in the internationally authoritative top-tier journal ACM Computing Surveys The paper directly addresses three core challenges in the field of visual privacy protection: the continuous expansion of privacy leakage boundaries driven by advances in computer vision technology, the increased complexity and reasoning capabilities of human visual perception that elevate protection difficulties, and the inherent conflict between privacy protection and information usability.
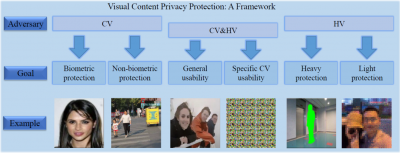
The study systematically reviews existing survey works that focus on specific privacy issues (such as identity recognition), specific application scenarios (such as social networks and surveillance systems), or specific technologies (such as machine learning and differential privacy), highlighting their limitations in coverage. This survey innovatively adopts a holistic macro perspective, breaking through single-dimensional constraints to construct a comprehensive framework that covers all visual content-related privacy issues and countermeasures.
Its core contributions lie in proposing a classification method and characteristics for visual privacy, constructing an innovative privacy protection framework, treating both computer vision and human vision as equally important sources of privacy risks, and systematically incorporating non-biometric features into the discussion of privacy protection. This work provides a clear knowledge map and development route for future research in visual privacy protection.
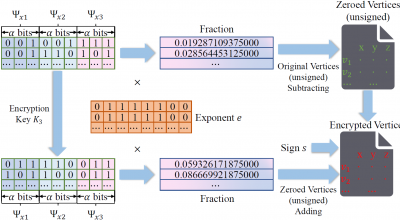
In the field of 3D object security protection, Dr. Zhao Ruoyu has also achieved groundbreaking progress. His paper, as the first author, titled "Lossless and Universal 3D Object Encryption With Differentiated Visual Effects Upon Decryption: A Novel Paradigm," was published in the prestigious CCFA journal IEEE Transactions on Dependable and Secure Computing.
The study proposes a novel paradigm for 3D object encryption. While inheriting the advantage of "layered decryption" to present differentiated visual effects, it successfully addresses two major technical bottlenecks of previous solutions: the inability to achieve lossless restoration and the high coupling of algorithms. By introducing a precision-preserving mechanism and a universal encryption interface design, this paradigm enables complete lossless recovery of 3D models after decryption and offers flexible compatibility with multiple encryption algorithms, significantly enhancing the practicality and universality of the solution.
Experimental results demonstrate that the proposed method excels in both operational efficiency and security robustness, paving a new technological pathway for secure transmission of 3D data, fine-grained access control, and applications in intelligent visual encryption.
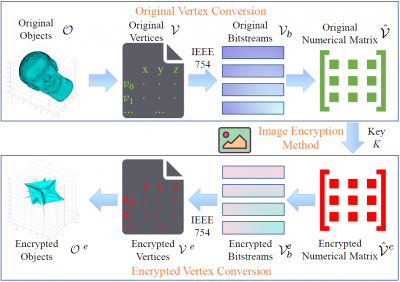
In response to the challenges of applying substitution-permutation paradigms to 3D object data encryption, Dr. Zhao Ruoyu, as the first author, published the paper "All Roads Lead to Rome: Achieving 3D Object Encryption through 2D Image Encryption Methods" in the CCFA journal IEEE Transactions on Image Processing. The paper proposes an ingeniously designed encryption framework.
The core innovation of this framework lies in converting the real-valued vertex sets of 3D objects into two-dimensional numerical matrices composed purely of integers. This transformation is analogous to the abstraction of high-level programming languages over low-level machine language, significantly reducing the design complexity of substitution-permutation encryption for 3D data. It provides a more concise and efficient operational platform for the diverse design and flexible implementation of encryption schemes.
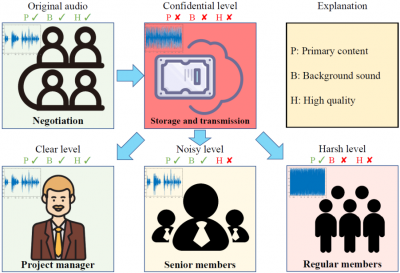
Dr. Zhao Ruoyu's research scope extends beyond the fields of images and 3D data. As the first author, his work titled "AES-AUDIO: An Encryption Scheme for Audio Supporting Differentiated Decryption" was published in the significant CCFB journal IEEE Transactions on Multimedia. This study proposes an audio encryption scheme named AES-AUDIO, which supports differentiated decryption.
By performing precise operations on binary floating-point representations of audio and designing a dedicated region-of-interest encryption algorithm, the scheme achieves the functionality of "one-time encryption, multi-level decryption." Users can decrypt audio into different auditory perceptual resolution versions—such as "confidential-grade," "coarse-grade," "noisy-grade," and "clear-grade"—based on their needs, effectively balancing the security and usability of audio content. The scheme has demonstrated excellent performance in both user experiments and security tests, providing an innovative solution for hierarchical protection and intelligent access control of audio content.
This series of research achievements by Dr. Zhao Ruoyu not only reflects his profound academic expertise in the field of multimedia security but also demonstrates his innovative capability in addressing critical scientific challenges. From theoretical foundations to technical implementation, these works have established a relatively comprehensive research framework, making substantial contributions to the advancement of related fields. The continuous emergence of his scientific accomplishments fully showcases the research strength of the School of Computer Science and Artificial Intelligence at JUFE, as well as the effectiveness of its cultivation of young faculty. This injects new vitality into the school's discipline development and talent cultivation efforts.